Rotating device helps study new wireless power transmission for electric vehicles Scientists from Tokyo Metropolitan…
INFRASTRUCTURE & TECHNOLOGY
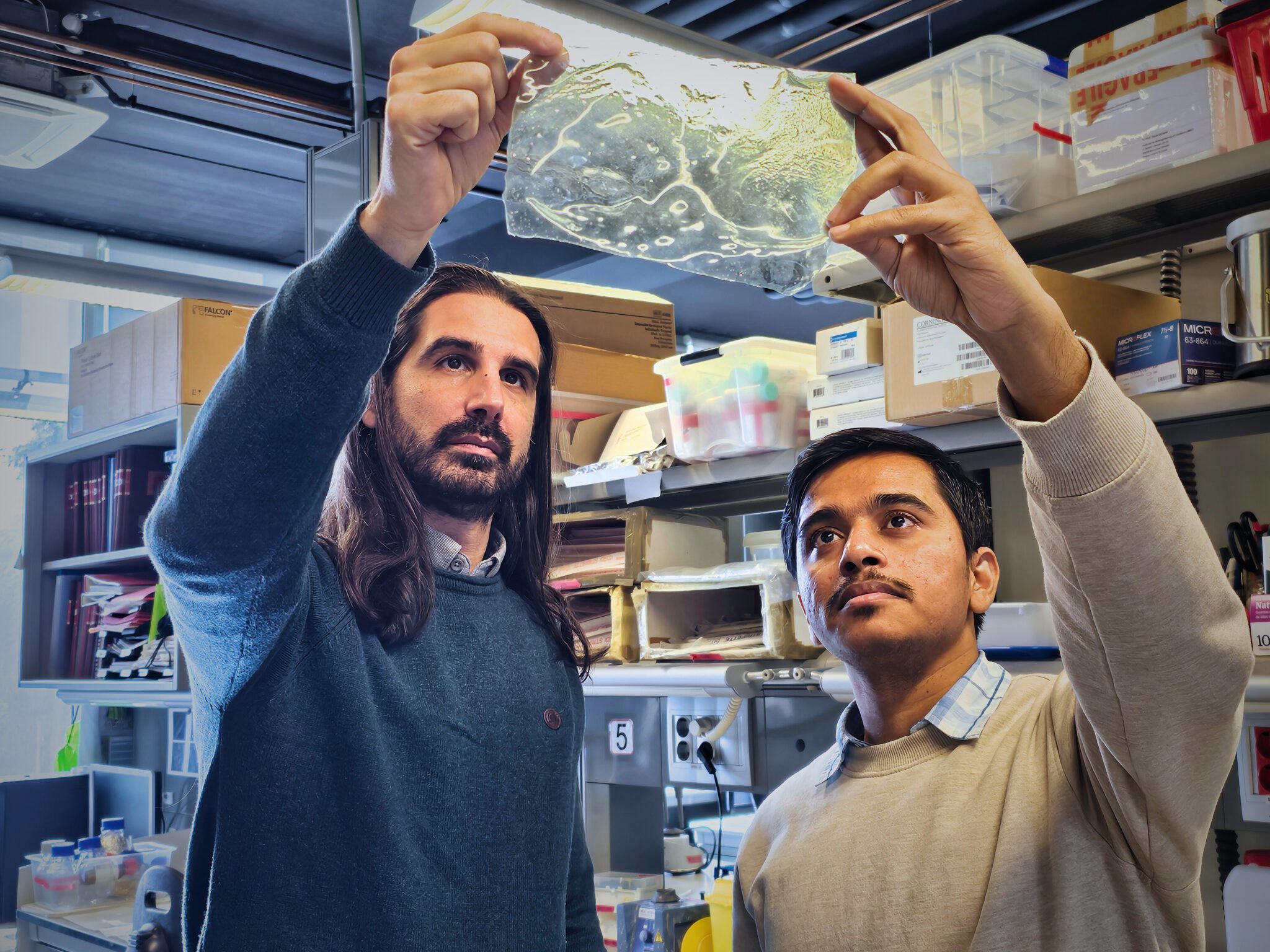
A new study has revealed how tiny imperfections and vibrations inside a promising quantum material…
The material is produced by the incorporation of nickel into the structure of chitosan, a…
Concrete gets a makeover with desert sand and plant-based additives The globe may be running…
On January 8, as thousands of Iranians took to the streets in nationwide protests, the…
Electric vehicles, batteries, wind turbines and solar panels (PV) are no longer just mechanical assets—they…
Imagine the internet suddenly stops working. Payment systems in your local food store go down.…
The U.S. competitive advantage in space depends on infrastructure hosted by allies. Editor’s Note: The U.S.-China…
The U.K. government’s latest attempt to access encrypted cloud backups could allow adversarial actors to…
Russian President Vladimir Putin, dressed in a military uniform, announced on Oct. 26, 2025, that…